Data is everywhere, supporting decisions and operations at different levels—both domestic and corporate. But this is only possible thanks to modern Data Centers like “Vinhedo 1” — the largest Data Center in Brazil and Latin America.
This robust facility is part of Ascenty’s extensive infrastructure. The company is the Latin American leader in the Data Center and connectivity market, ranking among the largest organizations in the world.
Below, we’ve prepared a complete overview with key information and curiosities about this giant of the Digital Era. Check out its role in the evolution of the market. Let’s dive in!
Vinhedo: The Largest Data Center in Brazil Belongs to Ascenty
The largest Data Center in Brazil is Vinhedo, owned by Ascenty. It was inaugurated in 2020 and remains the leader in size and digital infrastructure in the country and in Latin America.
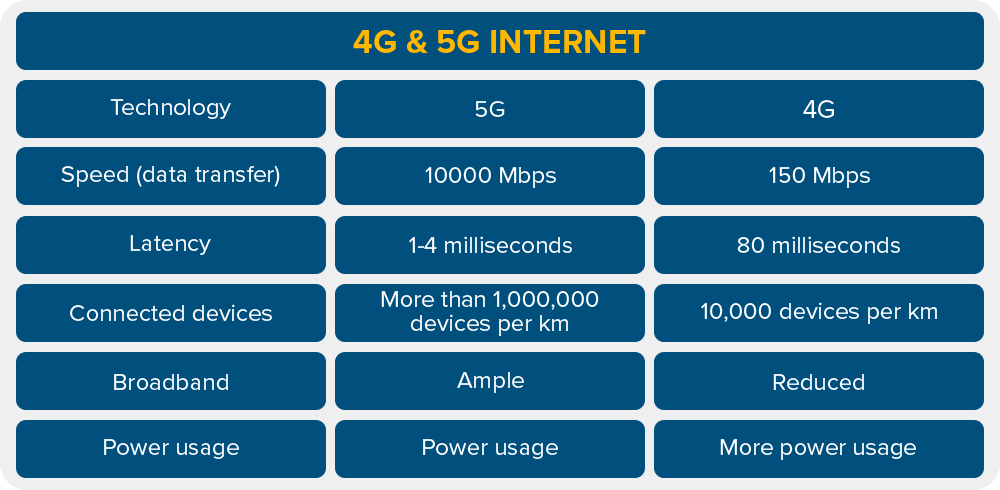
This ambitious large-scale project marked a turning point for the development of national companies. After all, the Data Center market was expanding and required upgrades to keep up with the arrival of 5G.
In this context, Vinhedo 2 was designed to support current and future demands of corporate Digital Transformation. To achieve this, it delivers the most modern and efficient data infrastructure available.
According to the latest report by consulting firm Arizton, Brazil is the largest Data Center market in Latin America, accounting for 50% of the region’s total capacity. Certainly, this result is strengthened by the efficient operation of this market giant.
Keep reading to discover some interesting facts and details about the facility!
Location
The largest Data Center in Brazil is located in Vinhedo, São Paulo state—just 70 km from the state capital. Its position is strategic: besides being close to the country’s main economic hubs, it provides multiple access routes to major highways and airports in the region.
Investment
The execution of this ambitious project required substantial investment. For the first construction phase, R$ 500 million were allocated to build a total area of 40,000 m² and a power capacity of 27 MW distributed across five infrastructures.
For Vinhedo 02, inaugurated in 2020, an additional US$ 150 million were invested, bringing the total power capacity to 36 MW.
Even after completion, Vinhedo continues receiving ongoing investments in modernization, maintenance, and personnel. After all, to ensure availability, security, and operational efficiency, infrastructure improvement must be continuous.
Total Area and Number of Racks
The Vinhedo Campus consists of two major Data Centers:
- Vinhedo 1
Operating since 2019
Total area: 21,000 m²
Racks: 3,300 - Vinhedo 2
Operating since 2020
Total area: 25,000 m²
Racks: 4,000
Certifications
Ascenty works daily to ensure operational continuity for clients and partners with maximum quality, reliability, and availability. Beyond the company’s proven credibility and expertise, it is recognized and certified by renowned international organizations.
Key certifications include:
- Tier III Design
- Tier III Facility
- TR3
- SOC 1, 2, and 3 for physical security and processes
- ISO 14001 for environmental management
- ISO 50001 for energy management
- Carbon Neutral certification
Energy Demand
Keeping the largest Data Center in Latin America running continuously is a challenge. Because it is a large-scale project covering a vast area, it requires significant energy to power cooling systems, networks, and all IT equipment hosted inside.
To meet this need, Vinhedo features a redundant Tri-bus substation, with three power lines feeding each module, as well as a backup diesel generation system with 48 hours of autonomy without refueling.
It’s also important to note that Ascenty prioritizes environmental responsibility and increasingly invests in building and operating green data centers — more sustainable and energy efficient.
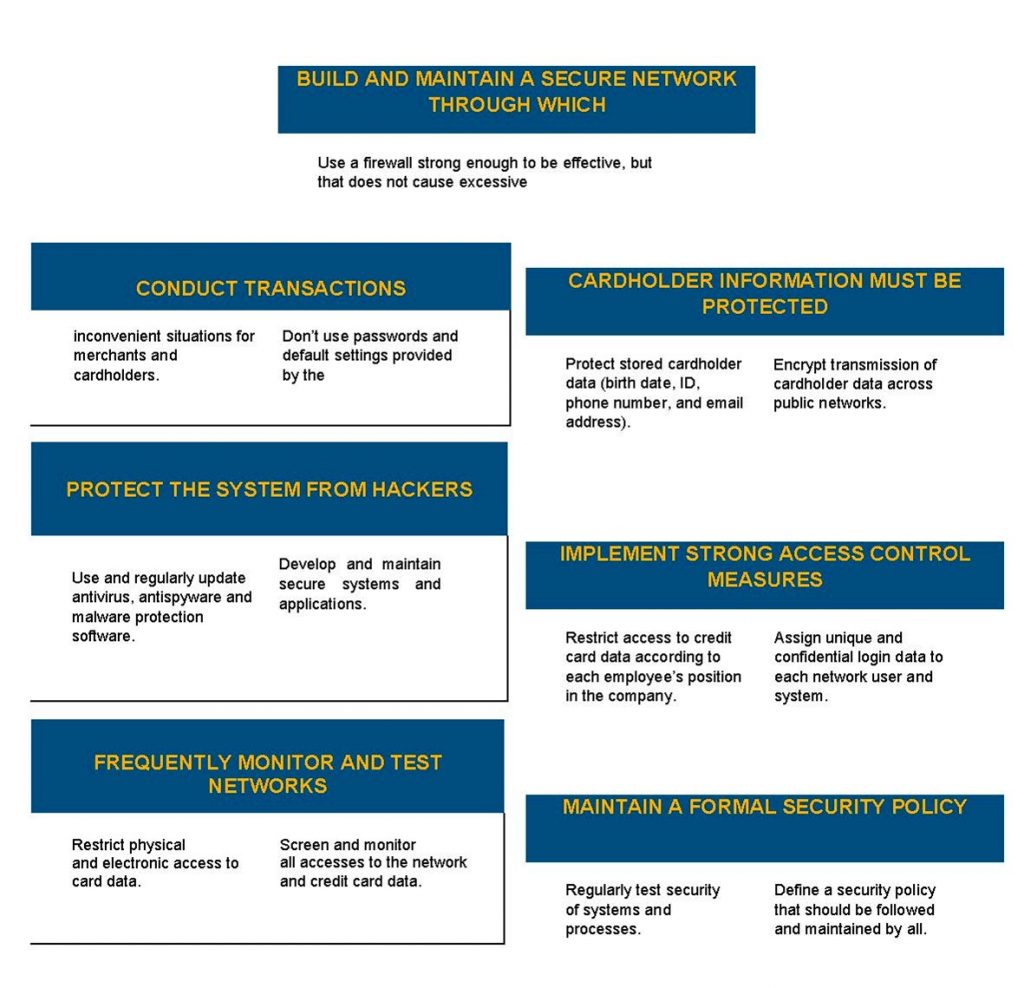
Security Features
From a security perspective, the largest Data Center in Latin America includes advanced protection features such as:
- 24×7 monitoring
- CCTV cameras with motion detection
- Digital recording and storage
- Access control with dual authentication: biometrics and magnetic card
Ascenty understands the value of data in today’s world and reinforces security so businesses can grow safely. This is one of the key benefits of Data Center migration and Colocation implementation.
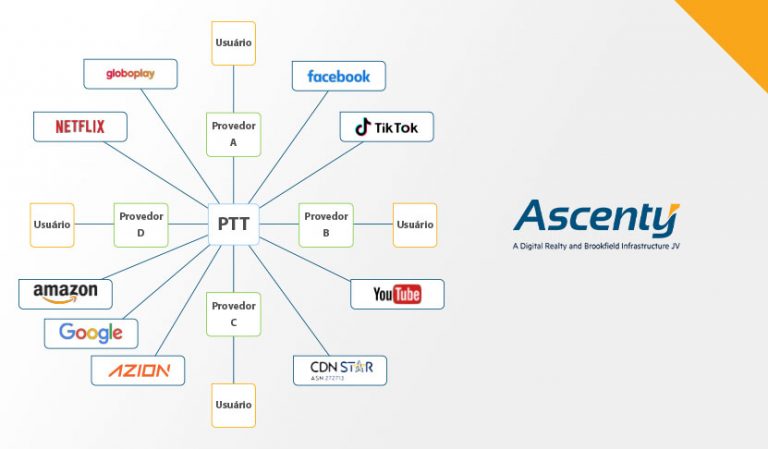
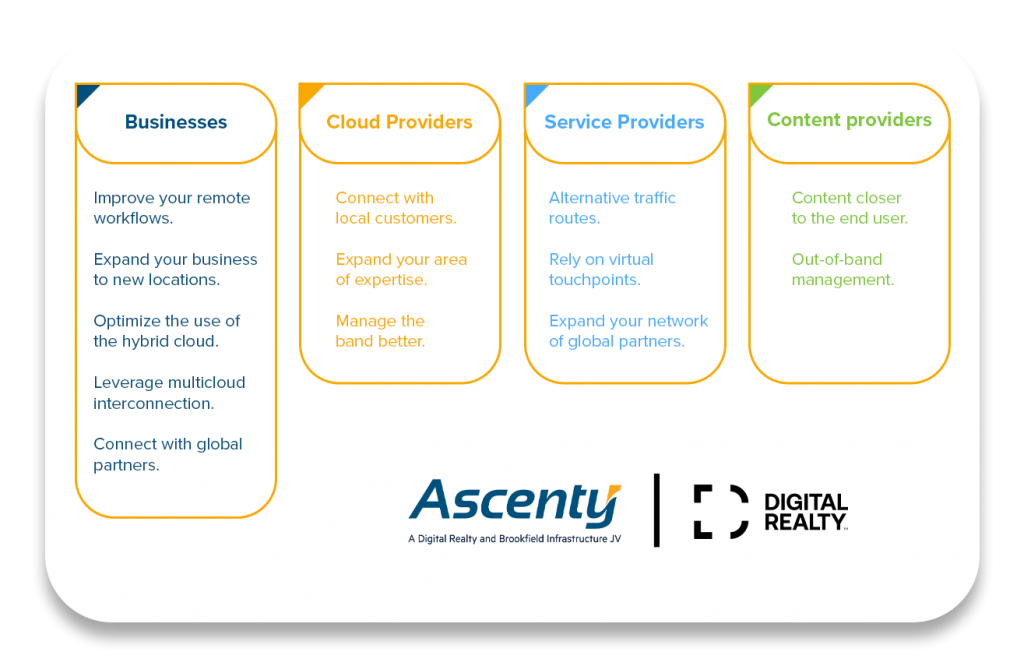
Connectivity Advantages
In addition to high‑quality equipment and redundant infrastructure, the Data Center delivers excellence in connectivity, low latency, and resilience. This is possible because the environment is linked by Ascenty’s own fiber‑optic network, connecting it to the world’s largest cloud providers.
Additionally, the infrastructure integrates with major telecommunications operators, enhancing network availability and ensuring service continuity for clients of all sizes.
What is the largest Data Center in Brazil?
The largest Data Center in Brazil is Vinhedo 2, from Ascenty. Located in Vinhedo (SP), it offers 25,000 m² of infrastructure and houses 4,000 racks. Together with Vinhedo 1 (21,000 m² and 3,300 racks), it forms the largest Data Center campus in Latin America.
Does Brazil have Data Centers?
Yes. Brazil is a major Data Center market in Latin America, with around 50% of the region’s installed capacity, according to Arizton. Companies like Ascenty lead this sector, with dozens of units across the country.
What is a Data Center?
A Data Center is a physical infrastructure designed to house servers, storage systems, and networking equipment essential for data processing and storage. These environments are highly secure, climate‑controlled, and monitored 24/7 to ensure availability, connectivity, and performance for corporate applications, cloud services, and more.
What is the largest Data Center in Latin America?
The largest Data Center in Latin America is also Vinhedo 2, by Ascenty. With world‑class infrastructure, robust connectivity, and international certifications, it stands out as a regional benchmark in digital infrastructure.
Ascenty: The Leading Data Center and Connectivity Provider in Latin America
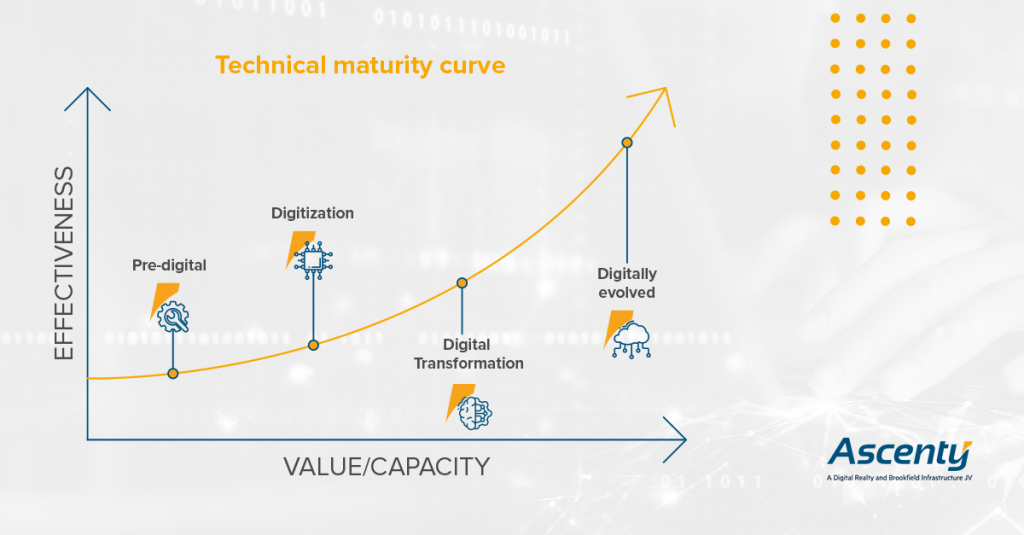
Founded in 2010, Ascenty offers a wide range of data center services to the market. The company serves the world’s largest cloud and technology providers, as well as clients in retail, finance, healthcare, industry, and IT integration services.
Reinforcing its commitment to innovation and Digital Transformation, Ascenty has the support of major partners and shareholders. In fact, the company is part of the Digital Realty group — the largest Data Center operator in the world, with over 300 facilities globally.
Looking ahead, Ascenty’s mission is to support the evolution of businesses today and in the future. The company currently has 38 Data Centers in operation and/or under construction across Brazil, Chile, Colombia, and Mexico — and the number keeps growing!
Beyond operating the largest Data Center in Brazil and Latin America, Ascenty reaffirms its commitment to delivering high‑quality, secure, and reliable solutions. After all, we are strategic partners—not just an infrastructure provider.
Recognition:
- Data Center Company of the Year in Latin America – Frost & Sullivan
- Environmental Impact Award – DCD Awards 2025
- 100% renewable energy and Carbon Neutral company
- Water‑free cooling operations
- 91.72% of waste diverted from landfills
- ISO 14001 (Environmental Management) and ISO 50001 (Energy Efficiency)
- 8 consecutive years in the NPS excellence zone
- SLA delivered with excellence and proactive support
Get in touch with our team and discover how we can help your company grow with advanced connectivity and cutting‑edge digital infrastructure!